Identity Providers Configuration
Overview
Identity Providers in Qalyptus Server enable single sign-on (SSO) authentication through integration with external identity services. In addition to built-in Windows authentication and email/password credentials, Qalyptus supports enterprise-grade authentication methods including SAML 2.0 and JWT tokens.
Supported Authentication Methods
- Windows Authentication: Integrated Windows credentials
- Email/Password: Built-in user accounts
- SAML 2.0: Enterprise SSO with identity providers (Okta, Auth0, Azure AD, etc.)
- JWT: Token-based authentication for API and embedded scenarios
Extension Compatibility
All four authentication methods are fully supported in Qalyptus Qlik Sense extensions: Qalyptus On-demand, Qalyptus Self-Reporting, and Qalyptus Notify, ensuring consistent authentication experiences across all platforms.
SAML 2.0 Identity Provider Configuration
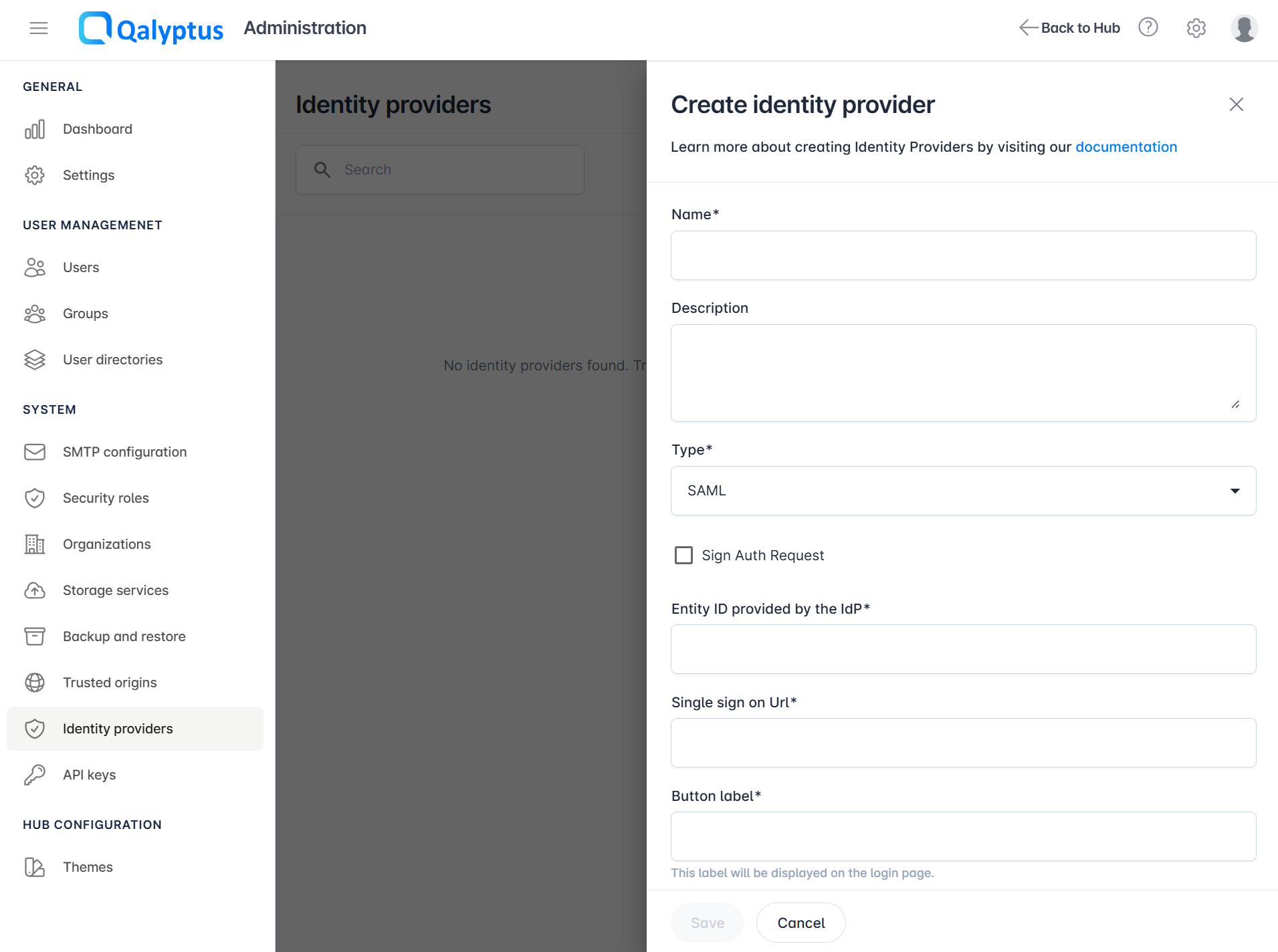
Creating a SAML Identity Provider
SAML 2.0 provides secure, standardized SSO authentication suitable for enterprise environments:
- Navigate to Qalyptus Administration > System > Identity providers
- Click Create Identity Provider and enter the information in the following fields:
- Name: Enter a descriptive name for the provider
- Description: Add optional details about the provider's purpose
- Type: Select SAML
- Sign Auth Request: Enable if your IdP requires signed authentication requests
- Use the provided metadata information in your Identity Provider settings:
- Assertion Consumer Service (ACS) URL: The endpoint for SAML responses
- Service Provider (SP) Entity ID: Unique identifier for Qalyptus Server
- Entity ID: Enter the Issuer URL provided by your IdP
- Single Sign-On URL: Enter the SSO URL from your IdP configuration
- Button Label: Customize the login button text (e.g., "Log in with Okta")
- Review all settings for accuracy
- Click Save to create the identity provider
The metadata file contains comprehensive Service Provider information. Most identity providers can import this file directly, automatically configuring the necessary settings.
For Ping Identity integration, configure the following attribute mapping:
Add the attribute Email Address with the value email in the Application settings.
Assignment and Usage
SAML Identity Providers must be assigned to specific organizations to control access:
-
Organization Assignment
- SAML providers are assigned to organizations
- Only organization members can use the assigned identity provider
- Multiple providers can be assigned to a single organization
- Navigate to Administration > System > Organizations, edit the organization, and select the Authentication tab. Then, choose the IDP to assign.
-
User Experience Variations
Multiple Providers: When an organization has multiple identity providers, users see login buttons for each option
Single Provider: With only one provider, users are automatically redirected to authenticate (no login button displayed)
Login Interface Examples:
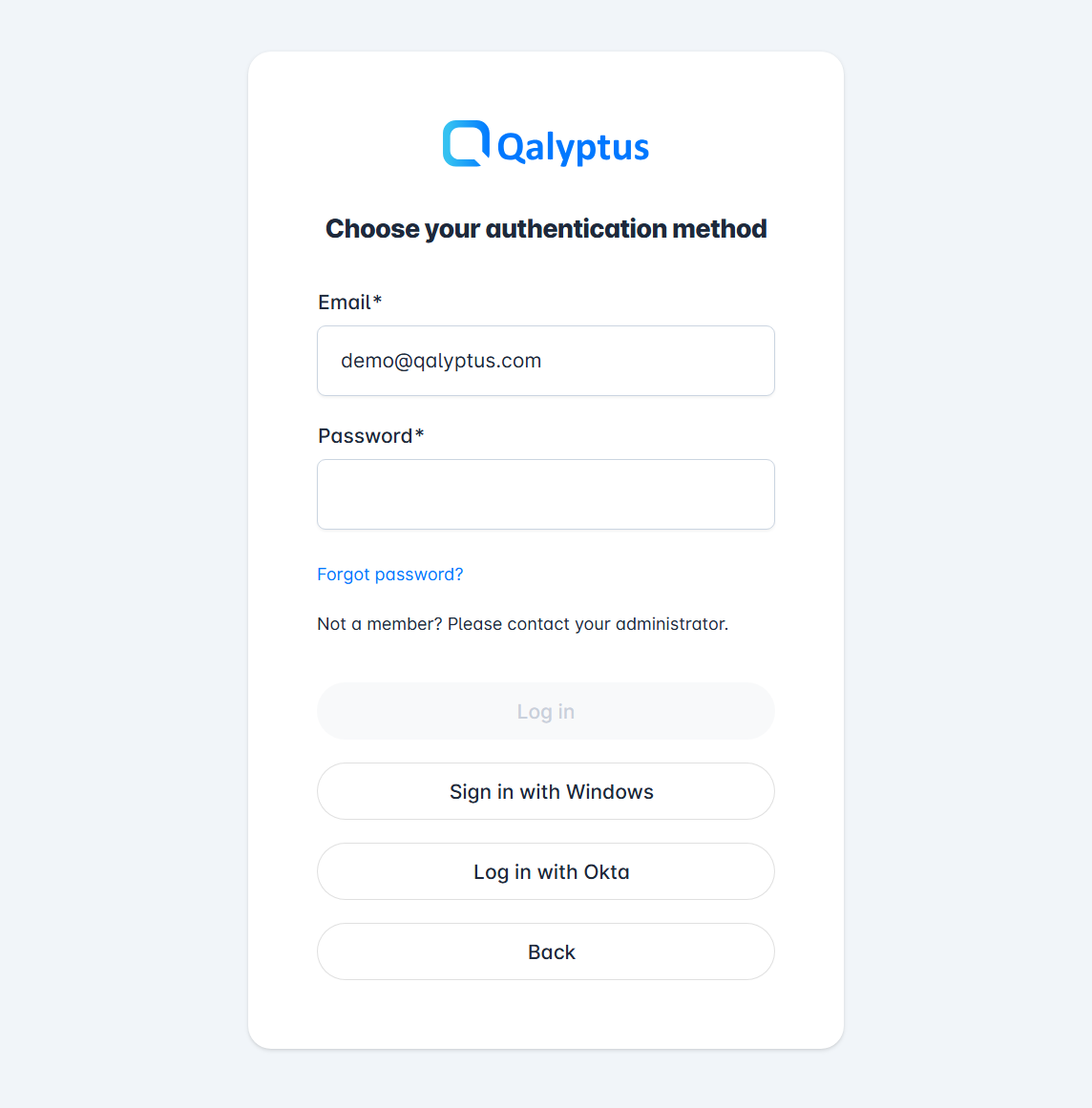
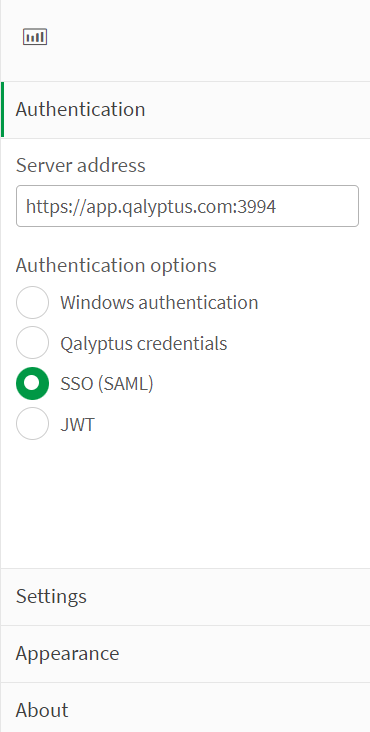
Extension Authentication: Configure SAML authentication in Qlik Sense extensions
JWT Identity Provider Configuration
Overview
JWT (JSON Web Token) identity providers enable token-based authentication for programmatic access and embedded scenarios. This method is particularly useful for API integration and custom application development.
- Only one JWT identity provider can be configured per Qalyptus Server instance
- JWT providers are not assigned to organizations - they have global scope
- Supports encryption algorithms: RS256, RS384, and RS512 only
Creating a JWT Identity Provider
- Navigate to Qalyptus Administration > System > Identity providers
- Click Create Identity Provider and enter the information in the following fields:
- Name: Enter a descriptive name
- Description: Add optional details about the JWT usage
- Type: Select JWT
- Certificate Public Key: Paste the RSA public key (see key generation below)
- JWT Attributes: Define the required JWT payload format (replace xxxxx with the user information)
- Review all settings
- Click Save to create the JWT provider
Key Generation and Management
Generate RSA key pairs for JWT token signing and verification:
Download OpenSSL from the official website and execute these commands:
# Generate a 4096-bit RSA private key
openssl genrsa -out privatekey.pem 4096
# Create a public certificate (valid for 5 years)
openssl req -new -x509 -key privatekey.pem -out publickey.cer -days 1825
Security Best Practices:
- Store the private key in a secure, encrypted location
- Use the public key content in the JWT identity provider configuration
- Implement key rotation procedures for long-term security
- Never share or expose private keys in configuration files
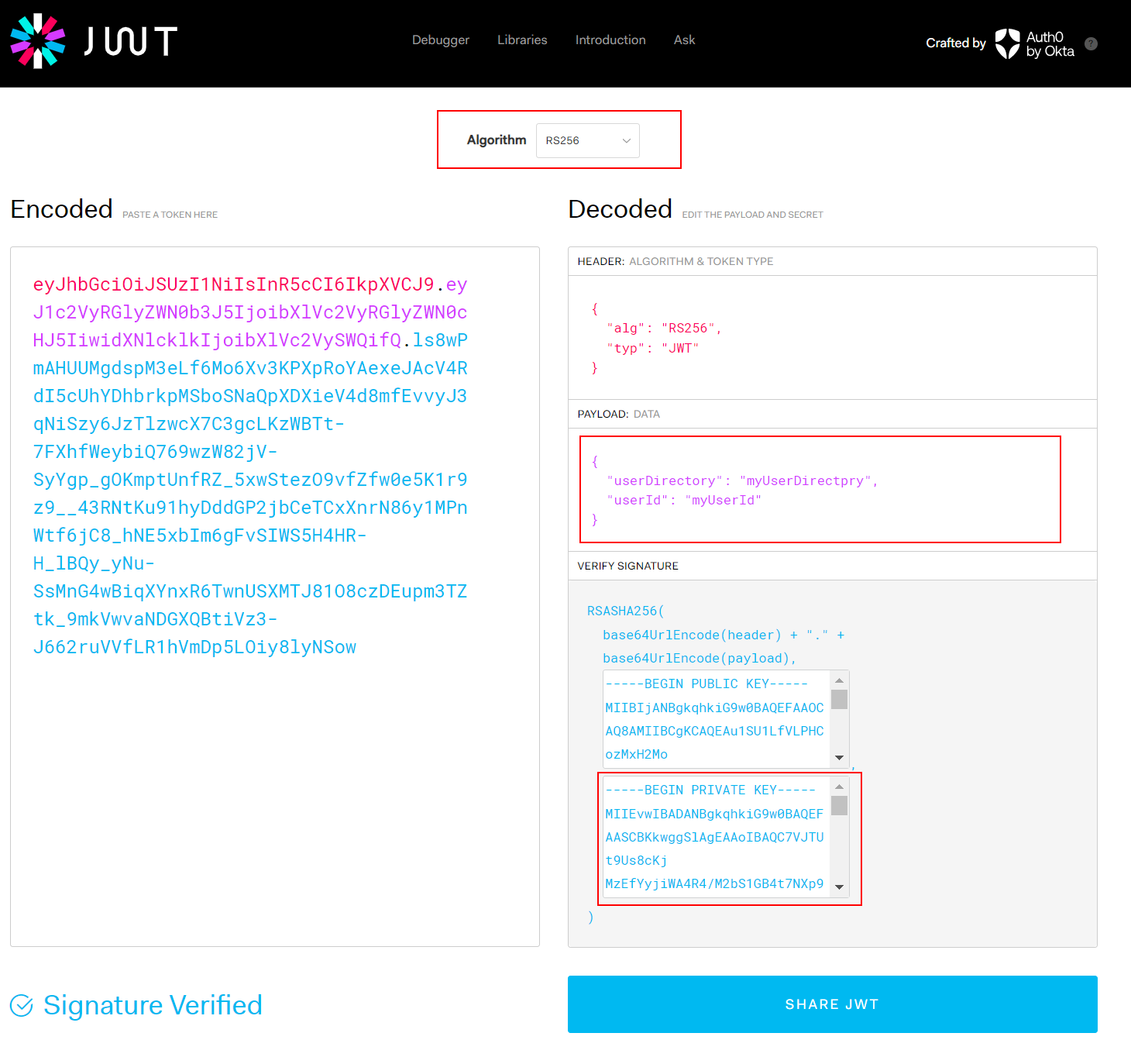
JWT Token Requirements and Usage
Token Creation Requirements
JWT tokens must meet specific criteria for successful authentication:
-
Required Payload Attributes
- userId: Must match the user identifier in Qlik Sense
- userDirectory: Must correspond to the Qlik Sense user directory
- Both values must exactly match existing Qlik Sense user account and the Qalyptus user domain account (userDirectory\userId)
-
Supported Encryption Algorithms
- RS256: RSA with SHA-256
- RS384: RSA with SHA-384
- RS512: RSA with SHA-512
-
Token Signing
- Sign tokens using the private key corresponding to the configured public key
- Ensure proper algorithm specification in the JWT header
Implementation Examples
JWT tokens can be created using various programming languages and libraries. Here's an example payload structure:
{
"userId": "john",
"userDirectory": "CORPORATE",
"exp": 1640995200,
"iat": 1640908800
}
JWT Creation Example (jwt.io):
API Authentication with JWT
Authenticate users programmatically using the Qalyptus Server REST API:
-
Authentication Endpoint
- Method: GET
- URL:
/api/v2/login/jwt-session - Authorization:
Bearer <jwt-token>
-
Request Example
GET /api/v2/login/jwt-session HTTP/1.1
Host: your-qalyptus-server.com
Authorization: Bearer eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9... -
Integration Scenarios
- Embedded Analytics: Seamless authentication in custom applications
- API Automation: Programmatic access for report generation
- Extension Usage: JWT authentication in Qlik Sense extensions
Configure JWT authentication for use with Qalyptus On-Demand, Qalyptus Self-Reporting, and Qalyptus Notify extensions in Qlik Sense applications and embedded analytics scenarios.
API Documentation: For complete API reference, visit the Qalyptus API documentation